Hacking a Bluetooth Smart Lock. IoT Series — How to properly conduct… | by Theodoros Danos | InfoSec Write-ups

Hacking a Bluetooth Smart Lock. IoT Series — How to properly conduct… | by Theodoros Danos | InfoSec Write-ups

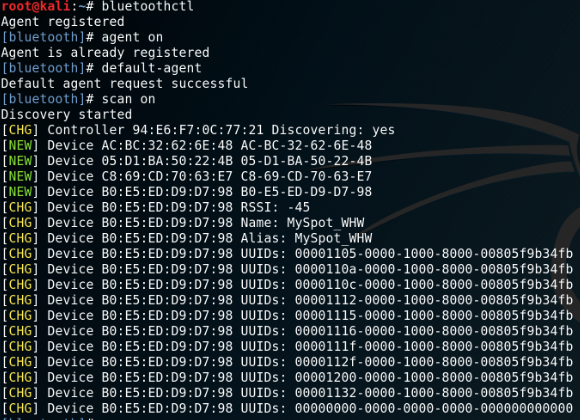
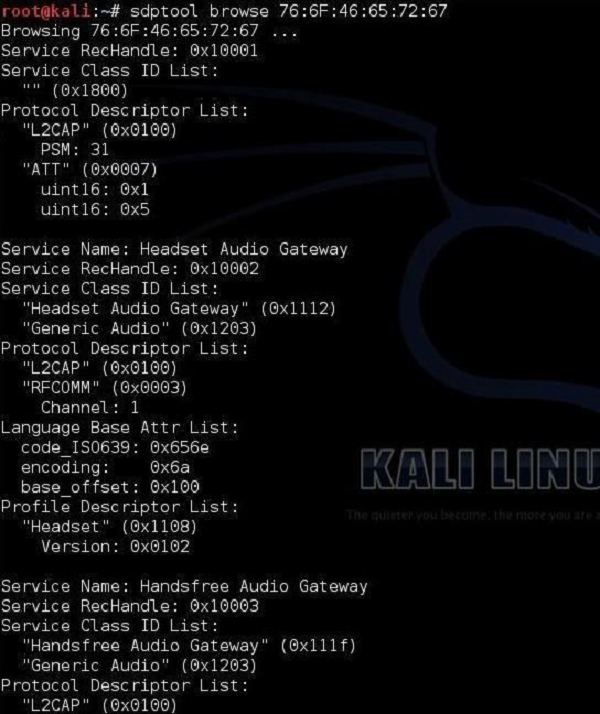
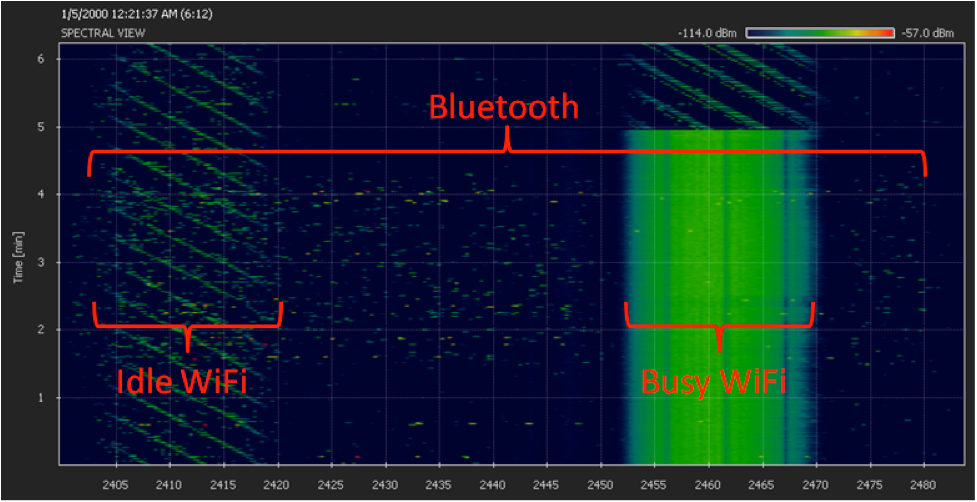
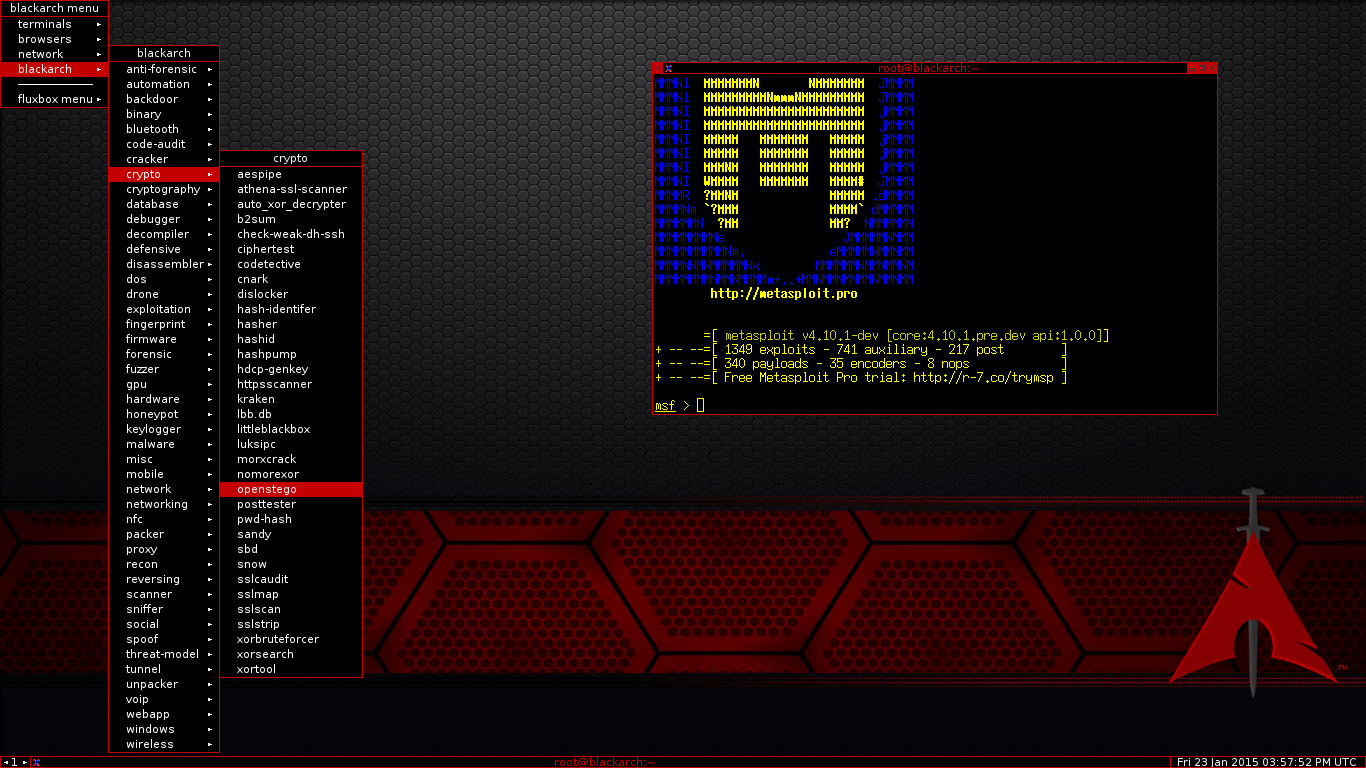
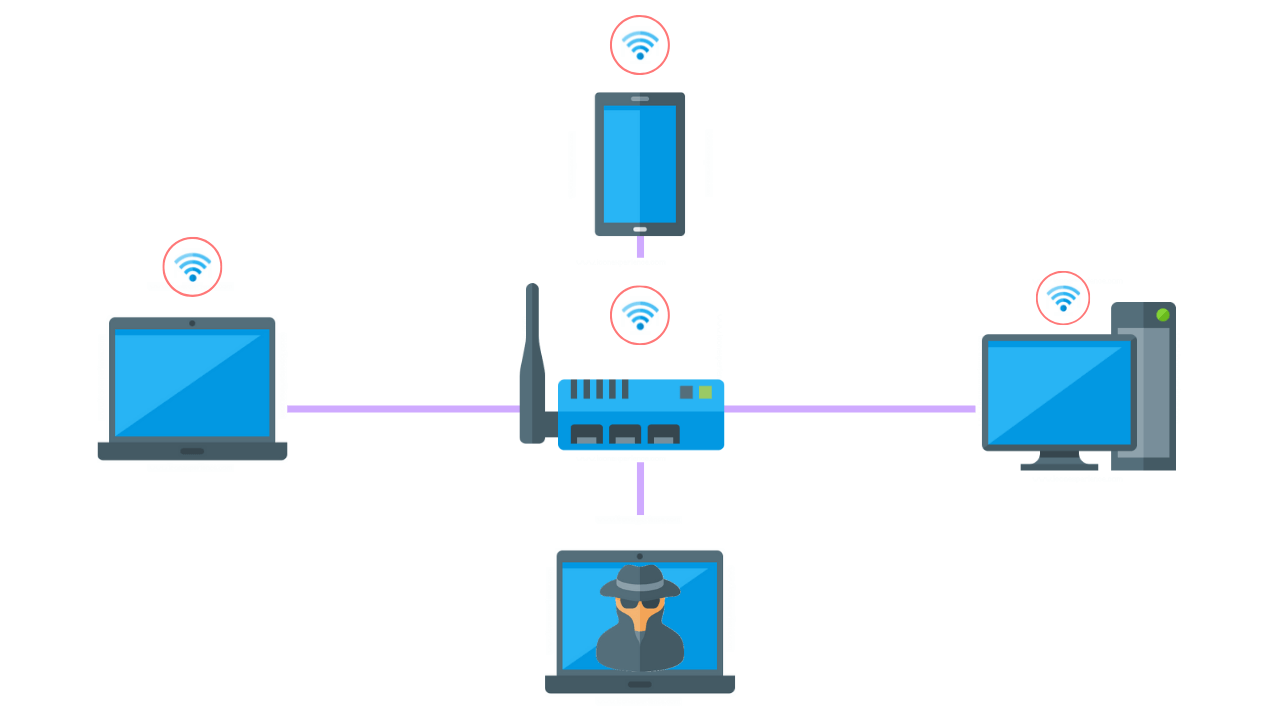
Bluetooth Security Levels | Bluetooth Penetration Testing | Offensive IoT Training Hacker Associate - YouTube








.png)